Testimony from Cassie Creswell from Raise Your Hands Action IL and  Parent Coalition for Student Privacy in front of the Illinois House Cybersecurity, Data Analytics, and IT Committee. News articles about these hearings and her testimony are posted here and here. Video of Cassie and other parents testifying is here.
Parent Coalition for Student Privacy in front of the Illinois House Cybersecurity, Data Analytics, and IT Committee. News articles about these hearings and her testimony are posted here and here. Video of Cassie and other parents testifying is here.
For Consideration By: Cybersecurity, Data Analytics and IT Committee, in hearing, August 7, 2018, at 10 AM.
Testimony for subject matter hearing on student data privacy
Thank you to the committee and Chairman Andrade for holding this hearing. My name is Cassie Creswell, and I’m the co-director of Raise Your Hand Action. We are a grassroots parent group that advocates for policy that supports a high-quality public education system for Illinois.
RYH Action continues to hear from parents about concerns posed by ever-increasing technology use and data collection in public schools. As you heard from the parents on the previous panel, the security and privacy of educational data is lacking.
CPS has had at least six major known data breaches since spring of 2015 with tens of thousands of students’ personal data, including in some cases health conditions and Individualized Education Program information for students with disabilities, improperly disclosed, and in several cases posted publicly on the web. A national database of publicly reported K-12 cybersecurity incidents includes at least 9 other instances in Illinois outside Chicago in the last two and a half years, including ransomware incidents.
We have also heard from parents about online surveillance, where students’ web history—and that of anyone they share a computer with—outside of school hours, off school grounds and off school-owned devices is being stored and monitored.
Parents are rarely told who their child’s data is being shared with beyond school walls and almost never asked for consent for that sharing. This data collection begins as early as preschool where teachers upload detailed records of children’s behavior to a third-party for-profit software vendor, including things like whether they hit another child, have a tantrum, wet their pants, etc.
Families who inform schools that they are not willing to have their child’s data harvested via apps and software have been told that there is no alternative way to receive instruction and even been told that they should consider private school or homeschooling.
Essentially, in order to receive an education, public school students are being forced to forfeit their right to privacy and a secure digital footprint.
Our group has attempted to advise parents how to navigate the aftermath of a data breach, how to respond to the school’s surveillance of their home computer or their child’s laptop, how to get info on what data is being collected via ed tech products or via surveys administered with state-mandated assessments or even via the software that has replaced college counseling services.
But this simply is not a problem that can be solved by individual parents armed with the advice from a parent group or privacy advocates.
Childhood is a time of growth, experimentation and development. The mistakes and challenges of childhood should not be part of a record that follows a child into adulthood and hamper the chance of future success. With the rapid pace of technological change, personal data that’s collected and shared today may have significant negative consequences in years to come.
And so, legislators must fully consider the implications of data collection, not only how data might be used in positive ways to enhance a child’s education in the present or near term, but how data might be used in negative ways in the long term. The convenience of tracking and recording every food item a fifth grader buys in the cafeteria for that child’s parent or the school or the food vendor should be balanced with the implications for that fifth grader, 20 years in the future who could be blacklisted for health insurance due to poor nutritional choices in the past. Detailed observations of behavior in preschool might be used for evaluating the effectiveness of preschool programs, but not if they risk being used for input to predictive algorithms for college admissions decisions.
Protecting student data encompasses a huge area of complex policy decisions. But there are some clear places to begin, and we think it’s imperative that the the following components are addressed in legislation next session:
- Full transparency: Operators, whether for-profit or non-profit, and whether selling a product or providing a product for “free” without a contract with a school or district, must all be subject to the same rules. Parents should know what organizations beyond the school district have possession of their children’s data, including government agencies, researchers, non-profits and companies.
- Freely given consent: Parents should be provided with an opportunity for informed consent before PII is transferred to any non-school officials. And this consent must be freely given: students and families must not be coerced into providing sensitive data to non-school official third-parties in exchange for a free and appropriate public education. The price of a public K-12 education should not be your personally-identifiable information.
- Control remains with the data’s owner: Even after consent is granted for data to be shared, control of the data must remain in the hands of students over 18 or parents of students under 18. Control means that the data can be reviewed, corrected and deleted at an owner’s request. And it means that consent for holding the data can be withdrawn.
- No Commercialization: Children should not be subjected to ads while using educational software nor have any of their online data used to target ads. SOPPA prohibited targeting ads based on stored profiles of children, but targeting ads to children in public schools based on data they are providing on the spot—their IP address, the particular e-book they are reading—is no more acceptable and should be prohibited. The push by Hobsons and the College Board to grant exceptions to the Student Online Personal Protection Act’s ban on targeted advertising and the sale of student profiles should be resisted. It wouldn’t be acceptable for a school counselor to accept payment for promoting a particular university or scholarship provider; it shouldn’t be allowed in career and college counseling software either. Student data should not be used to train or develop predictive algorithms for commercial software or apps.
- Security: The GA should establish detailed minimum requirements for how student data must be handled and how breaches are responded to and replace the vague “reasonable security procedures and practices” language in SOPPA. Districts should be held liable for not taking sufficient, reasonable precautions to keep data secure: encouraging the use of student ID numbers as usernames and passwords, using software that can create public webpages containing PII, storing health information on shared drives, collecting social-emotional survey data via google docs. Until districts are held responsible for negligent security practices, children will suffer the consequences.
- Privacy: Students own devices should not be surveilled, even if in use on school networks. And outside of school hours and school grounds, there should be no tracking of students–even on school owned devices. In addition, research has shown that de-identified or anonymized data research is an inadequate to protect privacy. The exceptions made in SOPPA for de-identified data should be removed.
Technological innovation in the field of education has promise, but that promise will be squandered if there is not parallel innovation in establishing norms for regulating information privacy and encoding them statute. This is not something that should be left to technology companies or school administration. Their interests in this area are to maximize profits in the case of the former and hold down costs in the case of the latter.
Right now, this leaves the onus of protecting our children’s digital footprint on parents. In fact, the onus is on you, our elected legislators, to serve as stewards of the public good by making sure that the cost of a public education in the 21st century is not our children’s right to information privacy.
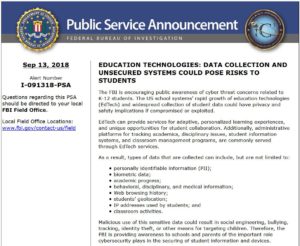 Internet Crime Complaint Center issued an important public service announcement (PSA) titled Education Technologies: Data Collection and Unsecured Systems Could Pose Risks to Students.
Internet Crime Complaint Center issued an important public service announcement (PSA) titled Education Technologies: Data Collection and Unsecured Systems Could Pose Risks to Students.

 80% of kids aged 6-12 watch YouTube yet parents are never asked for their consent before Google collects their personal data, as required by the federal law called COPPA.
80% of kids aged 6-12 watch YouTube yet parents are never asked for their consent before Google collects their personal data, as required by the federal law called COPPA.